In September, my son started junior high, and he craved having a smartphone. His lawn-mowing money was burning a hole in his self-made duct-tape wallet. So I googled for inexpensive options. Freedompop sounded like a great deal — free phone service (500 MB data per month), based on VoIP over cellular data. Too good to be true? Read on.
We ordered a Samsung Galaxy S4 that was supposed to take up to three weeks to be delivered. The website listed the phone as sitting in a “kitting” stage for the duration, and still no phone, and no follow-up email to tell us whether our order had disappeared into a black hole.
I couldn’t find a phone number for tech support, and there was no “live chat” option on the freedompop website, so I turned to Google, and they came to the rescue. I called, navigated a deep option tree, and eventually reached a live person, which was no easy feat. They told me the phones were on back order, and to wait another week or two.
So I did, with a very anxious son asking me daily about the order status. I showed him how to check the status himself. When two weeks had passed, I called again, and for the second time, I was told the phone was on back order, but it should be coming in the next week or two. Two weeks later, the phone finally shipped. My son was so excited to open the box and play with his shiny new device.
Knowing that smart phones love to consume data, we disabled most of the apps from using cellular data.
In the coming two weeks, I received emails from freedompop saying that cellular data had run out, and that I had been charged $10 to “top-up”. That was a surprise, so I disabled that feature, using their website.
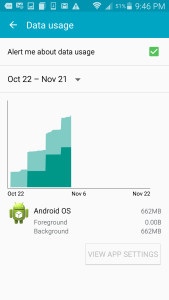
I opened the cellular data usage graph on the smartphone. It told me that the app known as “Android OS” had helpfully been chewing up the cellular data in large stair-step usage patterns. Android doesn’t allow us to disable cellular data for “Android OS”.
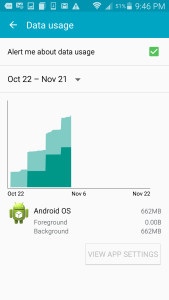
Apparently the high cellular data usage correlates with the downloaded of a 263 MB OS update over cellular. I recalled that we tried installing the update a few times, and it didn’t work because FreedomPop modifies the phone so that OS updates don’t install.
So the phone is caught in an impossible cycle, and the FreedomPop experience has been anything but a good one.
I submitted an email to their support system, which told me I would have a response within 48 to 72 hours. It’s been five days, and I’ve heard nothing further. I tried calling tech support, and after waiting on the line for 25 minutes, had to hang up.
What I thought we would save in cellular costs, I’ve paid for in time and top-up charges. The promise of “free” was too good to be true.
I wish we had chosen Ting, which has phenomenal customer service.